Transmission Log
Insights on Proactive Defence & Engineering.
Thoughts on proactive cybersecurity strategy, threat detection engineering, and resilient cloud architectures. Please note: All opinions and views expressed here are strictly my own and do not represent those of my employer or any other organisation.

The Zero-Luck Horizon: AI Acceleration and Mastering the Fundamentals
AI won't magically reshape technical attacks; it removes the friction from exploitation. In an era of instant software, luck-based security is mathematically dead.
Read Featured Article →Previous Transmissions

Overcoming Defensive Aperture Collapse: Full Activation in the Collision Space
In a technological era that demands rapid adaptation, taking the path of pathological caution is the ultimate risk. Security leaders must fully activate and build aggressively.
Read Article →
Security Leadership: Traits of Enablement vs. Anti-Traits of Friction
Why boards buy into leadership mindset, not just technical capability, and how to identify the anti-traits dragging down your security strategy.
Read Article →
Why Security Strategy is Slowing Down Engineering
And how to fix it by embedding operational empathy and product management principles.
Read Article →
3 Questions Your Board Should Ask the CISO About AI Risk
Move beyond hype and focus on pragmatic governance, data exposure, and model resilience.
Read Article →
The OpenClaw Dilemma: Agency Without Affordance
Agents that don’t need APIs break our existing security perimeters. If an AI can sign up for its own email, who owns its identity?
Read Article →
Epistemic Decay: The High Cost of Agentic Security
We are trading verified logic for probabilistic performance. Here’s why 'good enough' is a looming security crisis.
Read Article →
The Layer Zero Paradox: Why Foundational Security is Structurally Shallow
Why the giants of cloud and identity are architecturally incentivized to keep security shallow to prevent business friction.
Read Article →
The Automation Paradox: Over-Reliance on Security AI
How blind trust in AI alert triaging degrades analyst intuition and creates new blind spots.
Read Article →
The Milgram Trap: Why Synthetic Authority is the SOC's Newest Vulnerability
Why we are effectively automating the Milgram Experiment within our technical architectures, and what to do about it.
Read Article →
Dependency Gravity: The Axios Compromise
Analyzing the UNC1069 attack on axios and the systemic risk of 'Dependency Gravity' in modern software supply chains.
Read Article →
The Clean-Room Paradox: Generative Transmutation in Code Leaks
When source code leaks, traditional containment fails. AI assistants enable instant 'clean-room' rewrites, effectively transmuting IP into legally distinct forms.
Read Article →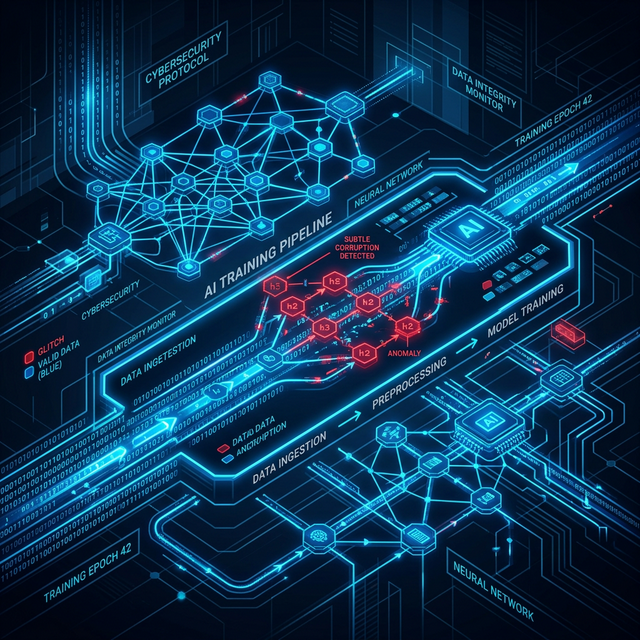
The Silent Threat: Data Poisoning in AI-Driven Security
Why the data feeding your threat detection models might be your greatest vulnerability.
Read Article →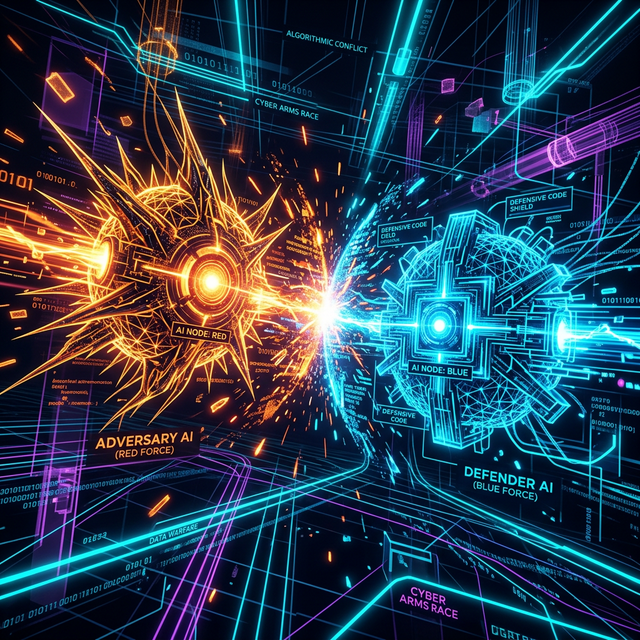
Adversarial AI: The New Arms Race in Cyber Offence
Defenders aren't the only ones using AI. How threat actors are weaponising machine learning.
Read Article →